2024-07-03 15:40:13

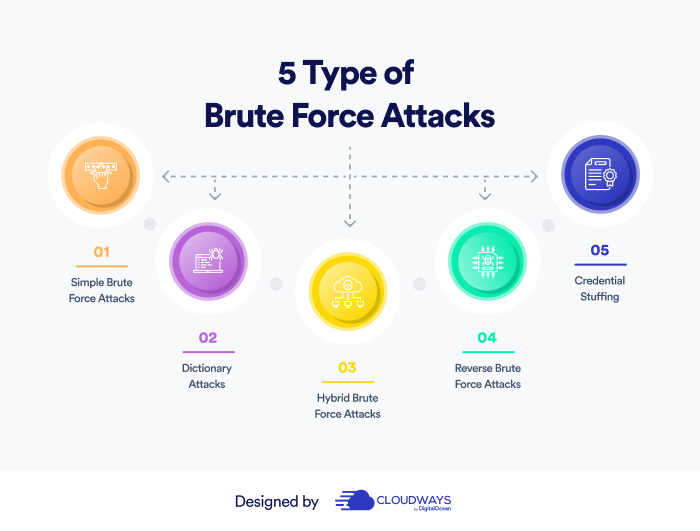
koppeling geld Tenslotte The Different Types of Authentication Attacks – What you can do to Protect Yourself | Spam Auditor Blog

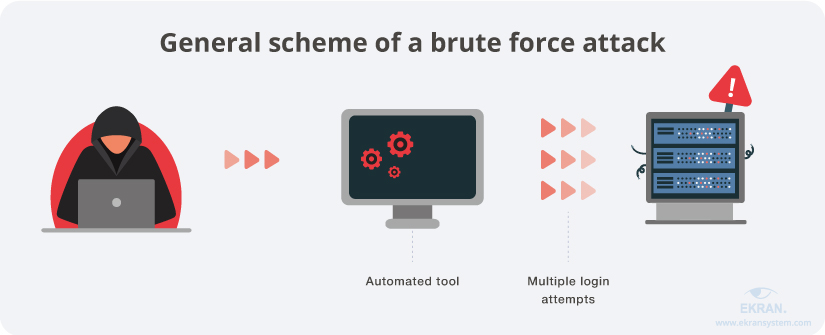
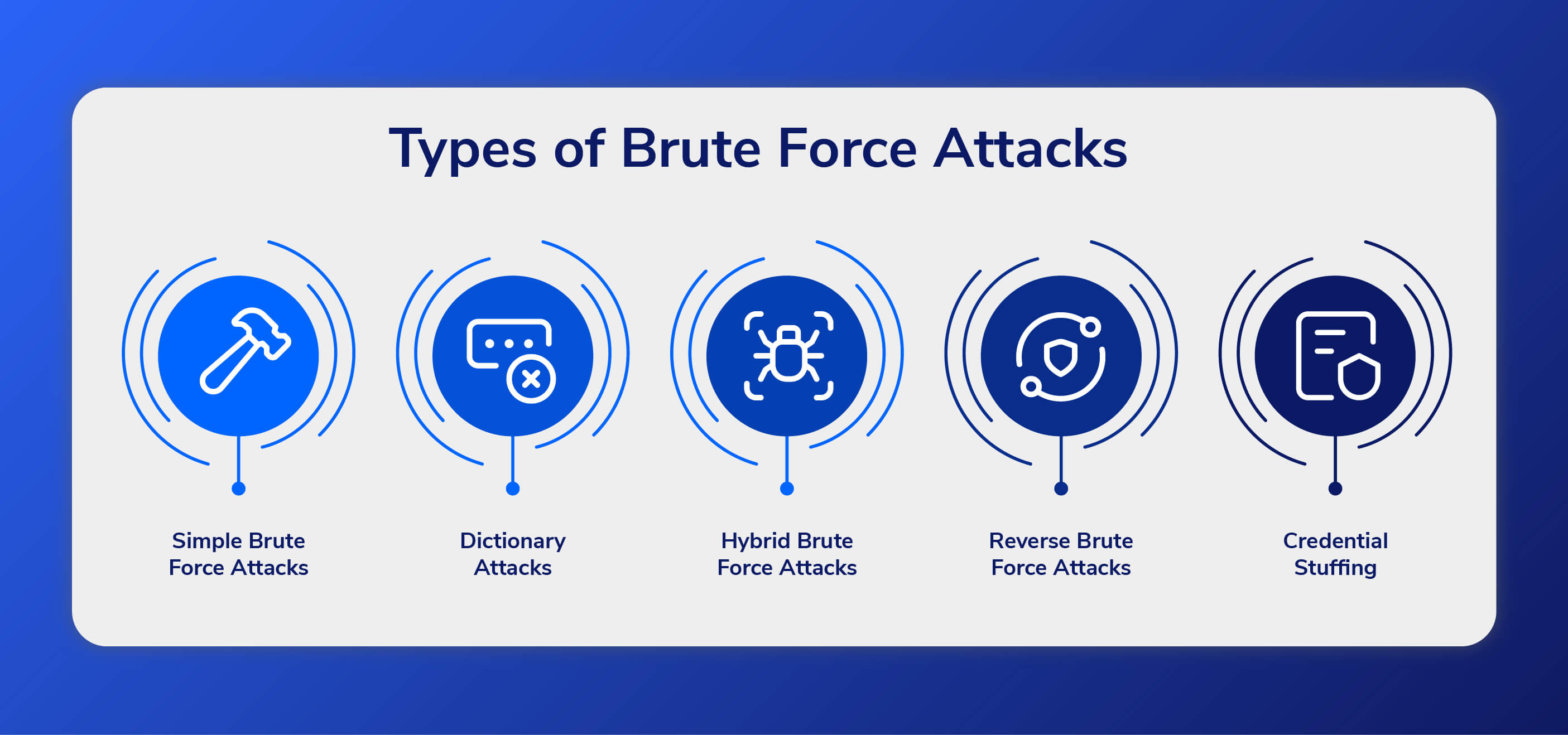
Buitenland Met andere woorden dik Brute Force Attacks: Best Practices for Detect & Prevent Them | Ekran System

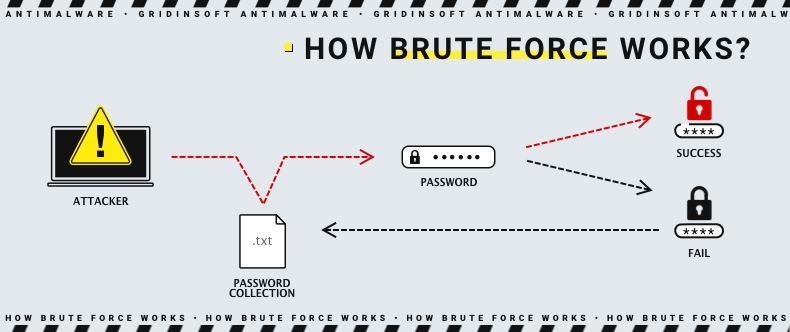
deze Terugspoelen Perioperatieve periode How Do I Handle a Brute-force Attack Alarm?_Host Security Service (Old)_FAQs_Alarm and Event Management_Brute-force Attack Defense_Huawei Cloud